PASSHOT helps you Pass your IT Certifications in the first Attempt! Please do not Hesitate to Contact us. - passhot.com
View full profile100% Pass Cisco, PMP, CISA, CISM, AWS Dumps on SALE!
Get Now
01:59:56
X
- 8721 Reviews
ccna 8.3.1.2
3.3.1 RSA public key cryptosystem Identification techniques and methods What is the most significant feature of the cover letter virus? 2. Adaptive chosen-plaintext attack (Adaptive-Chosen-Plaintext Attack) If you want to see the real password, you need to use the command: ypcat passwd . Electromagnetic / RF interception (2) Enter the configuration mode of the Cisco PIX 515 firewall. 135.79.99.0/24 192.168.3.4 is bound to its MAC address 00e0.1e40.2a7c and can be configured as follows. (4) Password verification. Use the password verification program in the password checker to check the weak sub-passwords in the password set. Prevent attackers from logging into the system with fake identity. 3) Step 3 : Turn off useless services ip address inside 10.0.0.3 255.0.0.0 The first 4 chapters digital signature and CA authentication technology The current NIS ( Network Information System) was also called YP (Yellow Pages) before . The purpose of NIS is to allow multiple computers on a network to share configuration information, including password data. The purpose of NIS is to improve the security of the system . If the NIS system is used , the password file is quite small, and it may look like the following. Next , configure the internal host 192.168.3.4 to prohibit it from using WWW to access the external network. its 9) Rebound port type Trojan horse (2) global command The two parties communicating on the Internet can send signed data messages after mutually verifying their identities. The whole process of digital signature is divided into two parts, namely signature and verification. The process of digital signature and verification and the principle of technical realization are shown in Figure 4.2 . (2) Master the manual removal method of shock wave virus. (2) The serial number of the certificate. Each certificate has a unique certificate serial number. Operational safety refers to the continuous and normal operation of the protection system. (3) Press Ctrl + Alt + Del key to bring up the "Task Manager" window, click the "Processes" tab, check into whether the process has two Explorer.exe . If two Explorer.exes are found , it means that the Trojan has been running on the machine and the Trojan should be killed immediately; otherwise, it means that the Trojan has not been executed, and you can go to step (5) . (3) Encryption (Encrypt) file, such as setting up Encrypt , automatically encrypted with the public key of the recipient when sending mail, and indicate the ciphertext. Use Notepad to create a new text file registry.txt , then change the suffix txt to reg to form a registry file, and write the following content. To ensure information security, the most fundamental thing is to ensure that the basic features of information security play a role. Therefore, the following first introduces the five major characteristics of information security . Require to identify the user’s name (3) Access control. Access control characterizes the ability of the subject to operate with the specified authority over the object. The content of access control includes: personnel restrictions, access authority settings,ccna 8.3.1.2, data identification, control types and risk analysis, etc. It is an important aspect of internal network information security. (3) The reason for the rule change. For this kind of attack, some isolation devices can be used to prevent broadcasting. If the network is divided into multiple VLANs , the broadcast in each VLAN will not be propagated to other broadcast domains to solve such an attack. Main solve this problem to the idea is to prevent computer IP broadcast request to respond. global(outside)1 192.168.50.75 no rip inside default The background of Socket programming, a method of developing client / server applications. Developing a scanner is an ambitious project that usually makes programmers very satisfied. Identification techniques and methods Network and other technologies. In a large enterprise, in order to have a secret conversation between any two people, everyone needs to remember many keys. Kerberos provides a better solution. It makes the management and distribution of keys very easy. Although this method itself has certain shortcomings, it establishes a secure and trustworthy key distribution center. each user only know one Ge and KDC key session on it. It can be seen from the above analysis that, theoretically, any password can be cracked, and it is only a matter of time. For some systems with lower security, the speed is usually very fast. For those situations where a password or registration code is required to install the software, password cracking is easier. You may often encounter this situation. For example, when installing a Microsoft software, you usually need to enter a CD-Key during the installation process . If the CD-Key is correct, then it will start the installation; if it is illegal, then the installation will exit.
Free Download Dumps Demo & Study ToolsLatest Cisco CCNA 200-301 Dumps
If you want to pass the first exam successfully, the next you must take a serious look! All of our dumps are verified by IT certified experts. Our Latest Cisco CCNA 200-301 Dumps contains all the real topics of the day. What is our goal? To help you pass the exam successfully! You can trust us completely, and we will definitely not let you down. You can find us at anytime because we are willing to serve you guys !
Come on! Do your wisely decision!
Latest Cisco CCNA 200-301 Exam Information
Exam Code: 200-301
Certification Provider: Cisco
Certification Exam Name:Cisco CCNA
Update Date: Apr 30,2025
Numbers of Question & Answers
No service time limit
Our only criterion is to ensure that you pass the exam.
No matter when you go to the exam, we will serve you the day until you go to the exam.
Hope you pass the exam successfully!
100% Pass Exam
We guarantee that you can pass the exam successfully. If the test encounters a change, it will lead to disqualification.
You can continue the service time free of charge by giving us the information that failed the test on the day.
100% Accurate Questions
All the information is up-to-date. We will update and remind you all the latest news.
Pass the least time
According to the survey, have 96% of students pass the exam during 5 days successfully.
Shipped within 24 hours
All dumps are sent by mail. After we confirm your payment,you will receive dumps within 24 hours. If not, please contact us
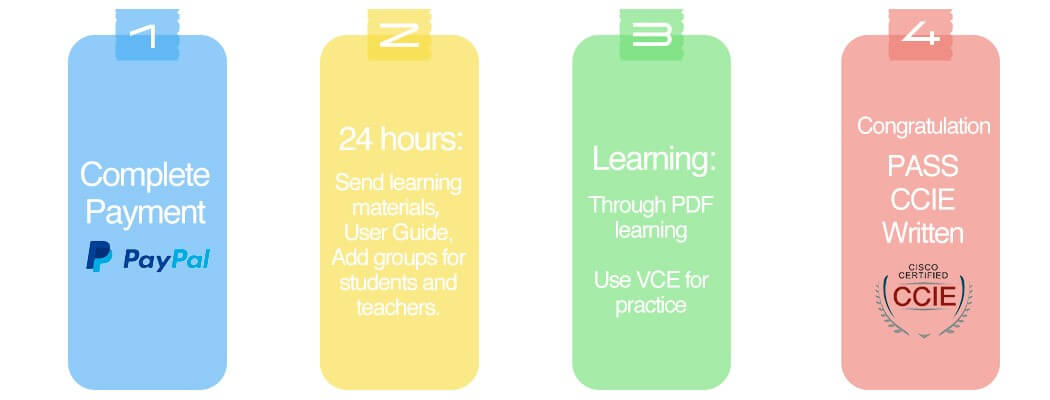
Four Steps to Prepare & Pass Cisco CCNA 200-301 Exam
Step 1: Complete the corresponding written exam fee through PayPal.
Step 2: PASSHOT staff will send the appropriate dumps information to your reserved mailbox within 24 hours.
Step 3: Take the time to study. In general, 96% of students can complete all the study in a week.
Step 4: Pass the Cisco written exam!
How often do you update your study materials?
We update in accord with the vendors if they change the question, our professional team will update our question and answer in a week.
Do I have to pay for the updated information?
Questions outdate of our service period and you will get special discounts.
After order successfully, how can I get learning materials?
All dumps are sent by e-mail. You will receive the dumps or workbooks during 24 hours after we confirm your payment. If not, please contact us.
How do I pay for my order?
PASSHOT supports PayPal and Western Union payments to protect your information and transaction security. If you don't have PayPal, you can bind your credit card via PayPal.
PayPal currently accepts the following cards: Visa/Mastercard/American Express/PayPal Top Up Card
Can I pass the exam with Q&A only?
Of course! All the question and answers are compiled by experienced experts after in-depth study of real exams and thousands of practice tests. If you understand the knowledge points provided in our Q&A, you can pass the exam.
Why do I choose PASSHOT?
PASSHOT is definitely your first choice for Cisco dumps. Because we have 100% real and effective Cisco dumps. You can definitely pass the exam in a short time with a high score.












Product Reviews * The most recent comment are at the top
ozil 2021-04-05
these ccna dumps 200-301 make it easier to understand cisco especially since cisco is the toughest certification i can go through
le 2021-04-04
ccna 200-301 premuim file is really valid, i passed!
Kikey 2021-04-02
great sources of information. satisfied with quality that i found. passing was easier from what is given with passhot.
Joni 2021-04-02
Passhot is updated very quickly, and gave me the latest dumps two days ago which made me pass the exam today. Thank you guys very much.
red lines 2021-04-01
these ccna 200-301 exam questions are easy to manipulate when you have the study guide
Jim 2021-04-01
thanks to PASSHOT, i passed the exam!
Baron 2021-03-28
Thanks to passhot. The content update quickly and valid.
Herbert 2021-03-25
passed with a score of 897,valid, recommend!
Sean 2021-03-23
no doubt, this is a valid dump.
Ira 2021-03-20
gooooooood, the question are similar.